I have seen dozens of Exchange 2010 deployments using wildcard certificates to publish OWA. Which works great, unless your trying to integrate Lync and your wildcard OWA!
The process of getting around this is pretty straight forward, but is not at straight forward coming up with the solution.
When configuring your OWA virtual directory for Instant Messaging you need to assign the certificate thumbprint you will be using
The problem is if you use the wildcard certificate you will not able to sign in to IM in OWA. you will see " Instant Messaging isn't available right now. The Contact List will appear when the service becomes available".
To resolve this we need to request another certificate from our Internal Certificate Authority to use strictly for this integration.
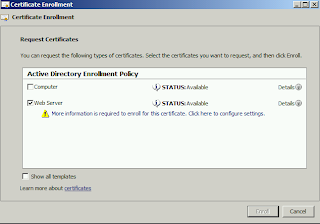
Go to MMC -> Add/Remove Snap-in and select Certificate. Select Computer. Navigate to Certificates -> Personal, right click Personal -> All Tasks and "Request New Certificate..."
If you do not have the "Web Server" template available. You need to add your exchange server to the certificate template as Allowed to Enroll under the Security tab.
Next specify the Trusted Application FQDN of the exchange server you used in your Lync Topology
Also you can add additional SAN names if your users use different FQDN to access OWA (internal and external)
Confirm the thumbprint of your new certificate
Apply the new certificate thumbprint to your owa virtual directory by running the following command
PS: > Get-OwaVirtualDirectory | Set-OwaVirtualDirectory -InstantMessagingCertificateThumbprint <New Certificate Thumbprint>
Just for safe measures, confirm the new thumbprint was added
And note that the certificate I'm using for OWA is still the wildcard! The new certificate is only being used for the integration, and not assigned to any exchange service.










great post !
ReplyDeletebut i guess this newly created certificate is just used for OWA and Lync to communicate right ? i mean will it work from outside your local network ?
You are correct, the certificate is only for OWA and Lync communication and is not published externally. You will continue to use your wildcard certificate for external access to OWA.
DeleteThanks for reading!
Hi
ReplyDeletei have did the same But the OWA integration not working.
The current Certifcate thumbprint matches with the subject name what is specified in lync
but the same error occurs
This comment has been removed by a blog administrator.
ReplyDeleteHey Tim,
ReplyDeleteSo I'm assuming this carries over for Exchange 2013/Lync 2013?
And what would you do around having multiple consolidated role Exchange servers in a DAG. Subject name as CAS Array/OWA URL with alternate names for each internal server FQDN and load it on each server?
Hi Shawn,
DeleteYes Exchange 2013/Lync 2013 integration is just as straight forward, apologies for no post as I have been swamped in Exchange projects and Lync has been on the back burner for the last few months. To poke more into your Exchange environment, any reason to have your server FQDNs on the SSL Certificate? Personally I would create the same namespace (mail.company.com) for both internal and external URLs, then do split DNS pointing mail.domain.com internally to your load balancer/DNS round robin, then externally to your public IP Address. makes your deployment much easier to manage and does not expose your internal server FQDN... Sorry to go on an Exchange rant :)
As for Lync2013/Exchange 2013 integration great TechNet Wiki article http://social.technet.microsoft.com/wiki/contents/articles/13168.integrating-exchange-2013-owa-and-lync-server-2013.aspx
Nice article! I couldn't get this to work, but then I remembered that I had modified the web.config file in C:\Program Files\Microsoft\Exchange Server\V15\ClientAccess\Owa to use the wildcard cert thumbprint. After changing the to the thumbprint value of the cert requested in your article, recycling the app pool with the following command: C:\Windows\System32\Inetsrv\Appcmd.exe recycle apppool /apppool.name:"MSExchangeOWAAppPool" and having a bunch of users mad at me for kicking them out of Outlook, OWA integration worked. Mix your article with the Microsoft article and it's easy as pie! https://technet.microsoft.com/en-us/library/jj688055.aspx
ReplyDeleteHi, thank you for this article.
ReplyDeleteI've followed the steps. and couldn't get it to work. I've checked everything, the web.config files on both CAS and Mailbox servers. For some reason, I couldn't see the thumbprint of the new certificate in there. Though, it is available in IIS Manager.
Any other tips?
Thanks.
I glad reading this post, thank you for updating and sharing useful article with us
ReplyDeleteWebsite Security Certificate | SSL certificate Prices | SSL Certificate Integration Service